Added Security for Twitter Users to Come Soon!

From spam to ham, Twitter deals with a lot of security issues on a daily basis. What about viruses/malware? I’m sure, yes. But, more importantly: account security. What do Twitter users need? Security assurance!
Therefore, Twitter is developing and perfecting a two-factor authentication method that will allow Twitter to not only ask for a password, but also a different credential to be sure of who is accessing your account.
From recent issues with Twitter accounts being hacked, it is best to have this in place, before it happens to other high profile organizations. Some of the recent organizations hacked were high profile including the Associated Press‘s account, CBS 60 Minutes account, and the BBC’s account.
Expect a shift in all online high profile websites switching to two-factor authentication. Apparently, it is the go-to emergency security solution.
Updated Details: Gozi Malware Back with More Money Stealing & Sophistication
It seems as if security firm, Trusteer, has identified a new variant of the Gozi financial malware. This one is more sophisticated and requires your attention. This new variant infects the Master Boot Record (MBR) on your computer — which is a boot sector software device that resides at the beginning of your hard drive that tells your computer how to boot up.
Just like TDL4, another MBR infector, this malware is hard to detect and remove. The main idea behind Gozi, though, is to wait for Internet Explorer to be launched on the victim’s machine, and malicious code is injected into the Process. This allows the malware to intercept web traffic, and inject its own code to webpages, misleading the user and collecting financial information (as well as social security numbers, birth dates, etc.).
Some speculate other developers have taken over, since apparently the main developer as well as accomplices were arrested not long ago. Looks like the new developers have a more sophisticated twist on the whole situation.
What’s different? The MBR rootkit component. This component makes the malware more sophisticated, because the removal of such threat can cause the computer to fail booting. The main problem at trying to fix infections in the MBR is that occasionally, the backup code that is placed in a different sector, is modified to not work when the infection locks in. This makes you have to keep it on the machine. However, it’s more effective to use private tools to help remove it.
One of the private tools, well sort of private, is the Kaspersky Rescue Disc. There are others that are available also, including TDSSKiller, which may or may not work out correctly.
If you need further help, we would love to assist. Please comment at any time!
Forty-Two (42) Whopping Security Holes Patched in Java
42 new security fixes are included for Oracle’s Java SE software. This new version with all security fixes included also includes a new feature to alert users of the dangers of running certain Java content.
Java 7 Update 21 was released yesterday (April 16, 2013) with all 42 bugs fixed. Most of the flaws are from exploits. Which means that visiting a hacked website can get you infected. Users running Java 6 are prompted to update to Java 7. However, Java 6 updates are still privately available (Update 45).
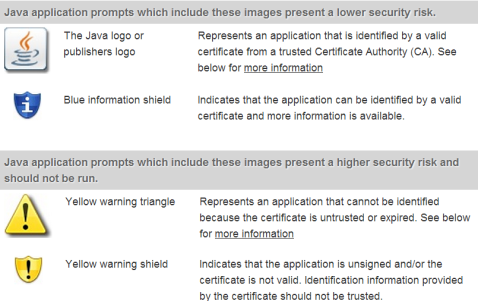
Anyway, the new update involves the introduction of newer security warnings as well as other message prompts. These are used for the web browsing environment to help users identify potentially risky content. See the image below for more information:
Java’s new features have been pretty continuous when Oracle finally realized last year that Java was getting to be an extremely insecure plugin. Java’s not so bad when it’s running an out-of-browser application, like a program or game.
The new version, now available on Java.com will bring the current version to Java SE 7 Update 21 and Java SE 6 Update 45. It is recommended to unplug your browser from Java, at least the main one, and only use Java Runtime Environment (JRE) in a lesser-used browser. Whenever you need to use a site that required Java, use it on your rare browser, so that you don’t get tripped up by ads or other exploit sites that try to access Java on your main browser.
Additionally, make sure to occasionally clear the Java cache, which will help prevent old temporary files for Java from loading. It’ll make the Java experience a bit better. This may also help remediate issues, if a Java application doesn’t run.
Facebook Home complicated with security problems: better wait!
Seems like Facebook Home, new launcher app for certain Android apps, will allow you to put updates from Facebook News Feed right onto your lock screen. While this brings Facebook to life for you, it isn’t exactly the safest. There are many reasons.
Let’s put it this way: adding a PIN code lock to your phone doesn’t keep people locked out of your Facebook account. People, even if they don’t access your phone, can still access the Facebook account on the lock screen, because the PIN code does not secure Facebook Home.
Maybe it’s a good idea to wait to use Facebook Home, so security features can be enhanced.
Do you have a phone enabled with Facebook Home and a PIN code? Let me know, comment below!
April Security Updates: Critically Patching Windows, Flash Player, and Shockwave Player
As usual for Patch Tuesday, many security updates were issued. I’m here to provide all the details for these critical updates. Not only did Windows get patched, but Adobe Flash and Shockwave Players did too.
Microsoft released a span of nine patch bundles, plugging security holes in Windows and other products. Separately, Adobe did its usual thing, and took part in Patch Tuesday as well for updates to Adobe Flash and Shockwave Players.
A cumulative update was made to Internet Explorer, which fixed two critical vulnerabilities present in almost all versions of Internet Explorer (in history). It should be noted that this includes IE 9 and 10.
There were many other updates for Windows worth noting.
Either you will receive Automatic Updates, if you’ve set Windows up to do so. Otherwise, go to Start, search Windows Update. Or for Windows 8, search for Windows Update on the Start screen.
Other than that, Adobe brings an update to Adobe Flash Player for Windows and Mac to v. 11.7.700.169. Linux should be updated to 11.2.202.280. Android 4.x+: 11.1.115.54 and 2.x-3.x: 11.1.111.50.
Keep in mind that Google Chrome and Internet Explorer 10 (Windows 8) automatically update Flash Player on their own.
Shockwave Player should be updated as well to v. 12.0.0.122! For these updates, go to www.Adobe.com
You should be able to update to Adobe AIR, which will help secure your computer even further from vulnerability. If you have Adobe AIR installed, which is required for quite a few programs that are built on its architecture (such as Tweetdeck, Pandora Internet Radio, games, etc.). AIR should automatically prompt to update.
Firefox 20 released, no more hanging plugins, 3 critical fixes
Firefox 20 was just released yesterday, marking also the 15th anniversary. 3 critical, 11 total security fixes are in Ff 20. Also, new private browsing updates were made as well as the ability to close hanging plugins without the browser hanging.
Mozilla detailed the security fixes, which includes the critical and high risk categories:
- CRITICAL: MFSA 2013-30 Miscellaneous memory safety hazards (rv:20.0 / rv:17.0.5)
- CRITICAL: MFSA 2013-35 WebGL crash with Mesa graphics driver on Linux
- CRITICAL: MFSA 2013-36 Bypass of SOW protections allows cloning of protected nodes
- HIGH: MFSA 2013-31 Out-of-bounds write in Cairo library
- HIGH: MFSA 2013-32 Privilege escalation through Mozilla Maintenance Service
- HIGH: MFSA 2013-34 Privilege escalation through Mozilla Updater
- HIGH: MFSA 2013-38 Cross-site scripting (XSS) using timed history navigations
Other than all that, there were more performance tweaks, as usual, as well as much improved HTML5 tools.
Mozilla is planning to fixes in Ff 21: known HTML5 video bug on being able to use copy actions, browsing and download history pairing, and function keys that don’t work when pressed. Other info on updates and issues, look here.
In Firefox, if you’re not automatically prompted to update, then do so as soon as possible by clicking the Firefox tab at the top left corner of the browser, hovering over Help >, click on About Firefox. You may also have to click Check for updates in the window that pops up. You should be patched.
Once you install Firefox, it will ask to restart your browser. Please allow it to do so, in order for it to finish updating and get you secure and well on your way in the dangers of the Internet.
Feel free to comment at any time.
US and South Korea Embrace Partnership before North Korea Prowls
South Korea, unbelievably will be stepping up partnership with the US, as North Korea becomes a more emerging threat (after declaring war late last week). Seems like North Korea, recently, has made its intentions known to attack the United States and South Korea. Although it may not seem like a large attack, we must still keep guard.
A news agency in South Korea identified that its defense ministry is planning to increase their forces and attempt to deter any further attacks. A customized deterrence strategy is in the works between the US and South Korea. Therefore, it plans to begin military drills sometime late this Summer (some are thinking August).
It’s hoped that South Korea could also aid as an ally, especially if it means the US has to battle North Korea in the future. Although this is like a small dog yapper trying to intimidate a big dog, a pre-meditated terror plot, like Al-Qaeda, is nothing to sneeze at.
The cyberwar continues to step it up little-by-little, but it seems like things have slowed a bit. Which is never a good sign, usually, because slowing down activity means that they are just meditating on a much bigger or more planned attack, and to take the US by surprise.