Forty-Two (42) Whopping Security Holes Patched in Java
42 new security fixes are included for Oracle’s Java SE software. This new version with all security fixes included also includes a new feature to alert users of the dangers of running certain Java content.
Java 7 Update 21 was released yesterday (April 16, 2013) with all 42 bugs fixed. Most of the flaws are from exploits. Which means that visiting a hacked website can get you infected. Users running Java 6 are prompted to update to Java 7. However, Java 6 updates are still privately available (Update 45).
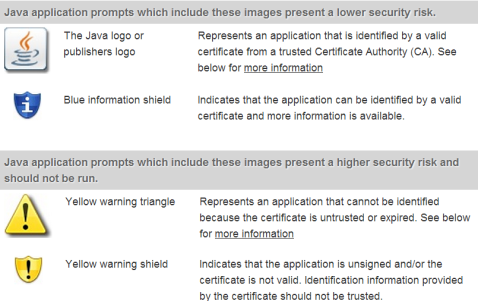
Anyway, the new update involves the introduction of newer security warnings as well as other message prompts. These are used for the web browsing environment to help users identify potentially risky content. See the image below for more information:
Java’s new features have been pretty continuous when Oracle finally realized last year that Java was getting to be an extremely insecure plugin. Java’s not so bad when it’s running an out-of-browser application, like a program or game.
The new version, now available on Java.com will bring the current version to Java SE 7 Update 21 and Java SE 6 Update 45. It is recommended to unplug your browser from Java, at least the main one, and only use Java Runtime Environment (JRE) in a lesser-used browser. Whenever you need to use a site that required Java, use it on your rare browser, so that you don’t get tripped up by ads or other exploit sites that try to access Java on your main browser.
Additionally, make sure to occasionally clear the Java cache, which will help prevent old temporary files for Java from loading. It’ll make the Java experience a bit better. This may also help remediate issues, if a Java application doesn’t run.
Oracle FINALLY Releases Critical Security Update for Java 7
New update now available, released by Oracle: Java 7, Update 11. Fixes a critical flaw, CVE-2013-0422. This update addresses the MBeanInstantiator in Java Runtime. It allows attackers to execute arbitrary code via loading unspecified classes.
A big response from security bloggers have sparked harsh criticism on Oracle. See information from Kafeine, ThreatPost, and Krebs. There are more bloggers talking about it. From what it seems, Oracle was rather stubborn about this, as they’ve been before.
The update is available via Java.com Web site, or can be downloaded from with Java via the Java Control Panel. Existing users should be able to update by going to the Control Panel and entering the Java Control Panel, or by searching for “Java” and clicking the “Update Now” button from the Update tab.
This changes the way that Java handles different applications. According to Oracle’s advisory: “The default security level for Java applets and web start applications has been increased from “Medium” to “High”. This affects the conditions under which unsigned (sandboxed) Java web applications can run. Previously, as long as you had the latest secure Java release installed applets and web start applications would continue to run as always. With the “High” setting the user is always warned before any unsigned application is run to prevent silent exploitation.”
Apparently, at one time, the issue was fixed. However, this was apparently ineffective. Many security bloggers say to just remove Java. Forget about it, if you don’t need it. It’ll save you time to update it (all the time!) and security trouble.
Oracle Revises Java: Prevent Apps from Running in Browsers + How to
The latest Java release, update 10 on December 11, allows users to restrict Java from running in web browsers. The newest version of the Java Development Kit, JDK 7 update 10, provides the ability to prevent any Java application from running in the browser. Since Java has been subject to so many security vulnerabilities and other miscellaneous attacks, this was the best move by Oracle.
It includes a good amount of security enhancements also, including the ability to set a specific level of security for any unsigned Java applets.
Some of the exploits seen in the past have made it clear that this was needed also for the unsigned Java applets. It calls for more default deny technology, which restricts quite a bit of features, but includes greater security.
That’s the biggest problem in applications and operating systems, is that developers do not want to suppress the features so much, but also don’t want a bunch of security threats. So, finding that balance is very important.
Allowing these new enhancements for the security of Java will help prevent a slew of Java attacks and keep people from turning away from Java. Most people will try to find alternatives if a plugin keeps getting attacked, e.g. Foxit Reader or Nitro Reader replacing Adobe Reader.
“The ability to select the desired level of security for unsigned applets, Java Web Start applications, and embedded JavaFX applications that run in a browser. Four levels of security are supported. This feature can be set in the Java Control Panel or (on Microsoft Windows platform only) using a command-line install argument,” Oracle said.
The final security feature released includes the ability to warn the user when the Runtime Environment (JRE) is out of date or below security standards.
How to enable this feature:
- Go to the Control Panel.
- Find the Java icon and double-click on it.
- Click the Security tab.
- Uncheck “enable Java content in the browser”.
Critical Java patch issued for 30 security holes
Oracle has issued a critical advisory for multiple (30) vulnerabilities in Java Runtime Environment. Most of the flaws involve Java Runtime Environment, however a couple of them are issued for JavaFX.
Here is our update table:
Version affected: JRE version 7 update 7 and previous => need update 9 now
Version affected: JRE version 6 update 35 and previous => need update 37 now
Version affected: JRE version 5 update 36 and previous => no patch available!
As always, you can get the latest Java updates from the following methods:
- WINDOWS = Access Start > Control Panel > Java. Click the Update Tab and select Update Now. (You can also enable automatic updates through this method)
- Any other method: http://www.java.com – click the Free Java Download. It should auto-detect your system.
NOTE: If you use the offline installer found on java.com, make sure you’re aware that it bundles either Ask Toolbar or McAfee Security Scan Plus. It isn’t recommended to install either one, but that choice is up to you.
Read more about different Java issues:
Report: Oracle databases vulnerable to hacking
A researcher showed today that Oracle’s databases could be hacked with brute-force attacks using only the database’s name and a username, according to Kaspersky Lab Security News.
Esteban Martinez Fayo, who works for AppSec Inc., was demonstrating his discovery at a security conference in Argentina and said that within just five hours on a regular PC using a special tool he could hack through easy passwords and access users’ data.
This isn’t the first time that security flaws have been found on Oracle databases. In January, the company squashed 78 software bugs in a major patch that stemmed from a flaw that allowed hackers into its databases remotely. And, just last month, new vulnerabilities that can be exploited to run arbitrary code were discovered in Oracle’s latest Java 7 update.
Java releases Update 7 for Java 7, and Update 35 for Java 6
Oracle did what all of us were hoping they would do – release an out-of-band patch for the latest Java zero-day vulnerability. The new version of Java, 1.7.0_07 and 1.6.0_35, both fix the vulnerabilities mentioned in CVE-2012-4681.
If you need Java we recommend that you install this update immediately. If you have no need for Java we recommend that you uninstall Java all together instead if you haven’t already done so. More information from Oracle about the vulnerability and patch is available in their security alert.
Information obtained from Websense and other communities.
Patch Tuesday This Month Was a Huge Hit!
Patch Tuesday this month (June 2012) was quite a show of vulnerability patching.
From Microsoft Updates to Oracle Updates!
Oracle Updates
Java Standard Edition needed patched big time, Oracle notes. 14 vulnerabilities were found recently, which ensured the update. It is recommended to patch immediately from Java.com, because six of the vulnerabilities received the highest possible common vulnerability scoring system (CVSS) rating.
If 12 out of 14 vulnerabilities stay unpatched, they are remotely exploitable, which means they present a HUGE security risk!
This update addresses security vulnerabilities in the Java development kit (JDK) and runtime environment (JRE) version 7 update 4 and earlier, JDK and JRE version 6 update 32 and earlier, JDK and JRE update 35 and earlier, JDK and JRE 1.4.2 update 37 and earlier, and JavaFX 2.1 and earlier.
Oracle gives credit for reporting these vulnerabilities to Adam Gowdiak of Security Explorations, Andrei Costin of Secunia, Chris Ries of TippingPoint, and Clayton Smith of Entrust.
Microsoft Windows Updates
3 critical updates – 4 important updates = 7 total bulletins that were addressed.
Here is a rundown of the critical updates:
- MS12-036 – remote desktop vulnerability: an attacker could obtain the credentials to perform attacks through the Remote Desktop Protocol (RDP).
- MS12-037 – cumulative security update for Internet Explorer…addressed 1 public and 12 private vulnerabilities.
- MS12-038 – This is a .NET Framework issue in XAML browser applications (XBAP), where an attacker can execute remote code if credentials are right.
Overall, Patch Tuesday this time around was a huge hit.
Now, get to work on the updates: